RedEye, an open-source analytic tool for operators to visualize and report C2 activity, was announced by the United States' Cybersecurity and Infrastructure Security Agency (CISA).…
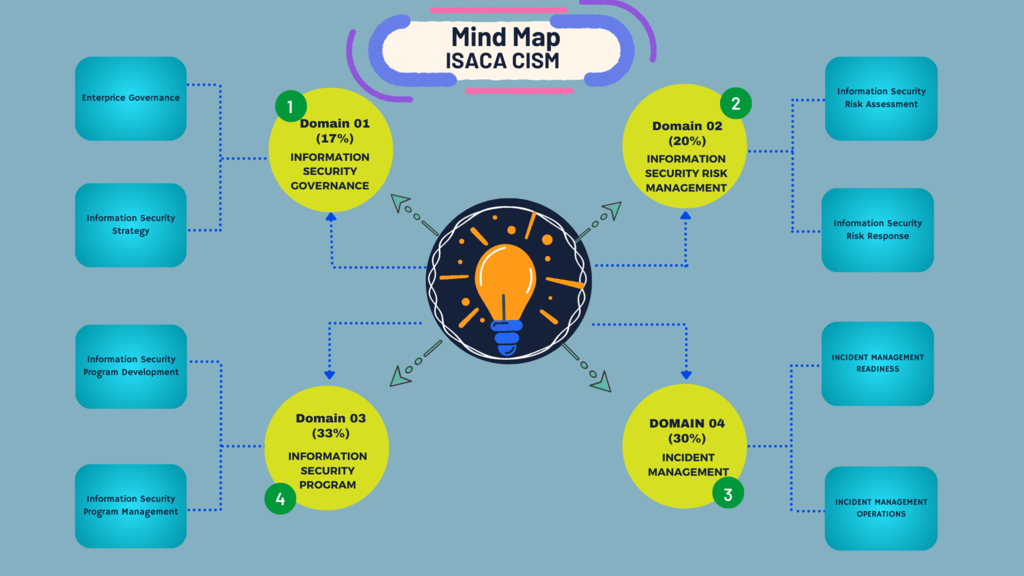
Security risks increase in tandem with the development of new technologies. The discipline of cybersecurity is evolving rapidly in response to new risks. These are…
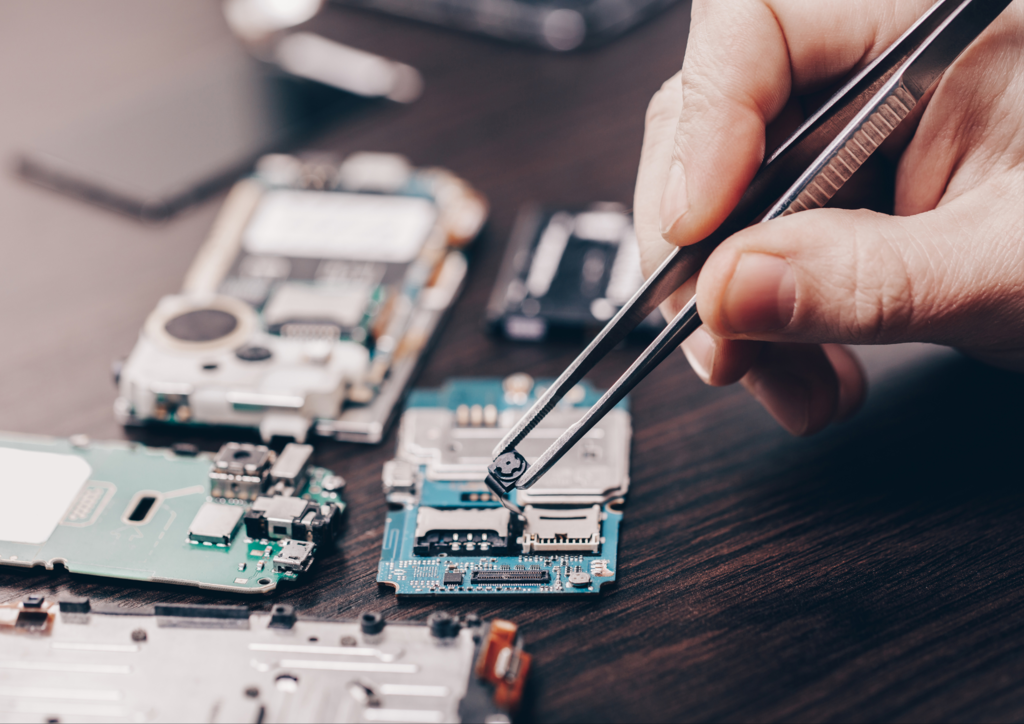
Manufacturers are fortifying operational technology and vehicle platforms to close down high-risk vulnerabilities, ISG Provider Lens™ report says STAMFORD, Conn.--(BUSINESS WIRE)--Increased automobile and industrial operational…