Sed condimentum massa in enim cursus, sed mattis elit malesuada. Lorem sapien acveh icula vestibulum, arcu magna aliquet velit. Nunc elementum mattis diam eu aliquam.…

When CISA discovered what it believed to be advanced persistent threat (APT) activity at a Federal Civilian Executive Branch (FCEB) entity between the middle of…

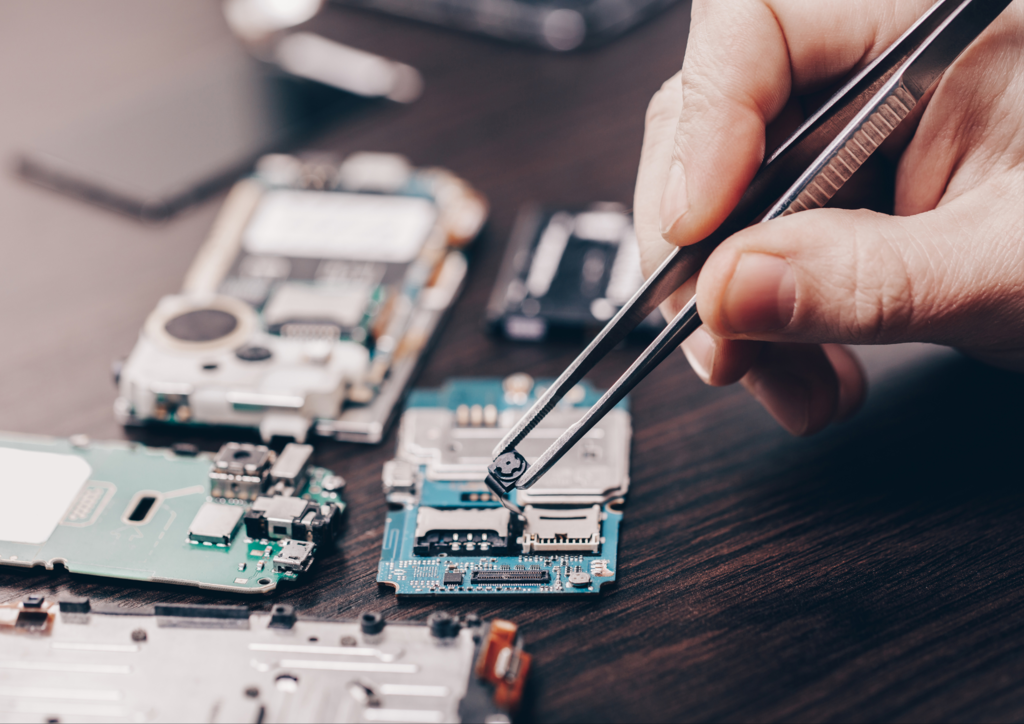
SIM or Integrated Circuit Card (ICC) is a microcontroller‐based smart card that stores important data including all the listed below Integrated circuit card identifier (ICCID)…